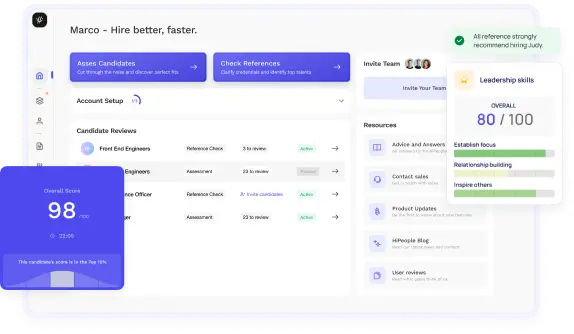
Streamline hiring with effortless screening tools
Optimise your hiring process with HiPeople's AI assessments and reference checks.

Are you ready to ace your Linux admin interview and secure your dream job in the world of Linux administration? Whether you're a seasoned professional looking to advance your career or a newcomer eager to break into the field, mastering the interview process is essential for success. In this guide, we'll delve deep into the realm of Linux admin interview questions, covering everything from technical skills and problem-solving abilities to soft skills and communication strategies. With practical tips, detailed explanations, and real-world examples, you'll gain the confidence and expertise needed to impress interviewers and land your ideal role as a Linux administrator.
Before delving into the interview process, it's essential to have a clear understanding of the Linux administration role. Linux administrators play a critical role in maintaining and optimizing Linux-based systems, ensuring their stability, security, and performance. Here's an overview of the key responsibilities and skills required for Linux administration:
Interviews play a crucial role in selecting competent Linux administrators who possess the necessary skills, knowledge, and attributes to excel in the role. Here's why interviews are important:
Overall, interviews serve as a crucial step in the selection process for identifying competent Linux administrators who possess the technical skills, soft skills, and attributes required to thrive in the role and contribute to the success of the organization.
As you embark on your journey into Linux administration, it's crucial to have a solid understanding of what the role entails. Let's delve deeper into the intricacies of being a Linux administrator.
A Linux administrator is essentially the guardian of the Linux-based infrastructure within an organization. They are responsible for maintaining the integrity, security, and efficiency of Linux systems, ensuring that they meet the operational needs of the business. Linux administrators oversee everything from server setup and configuration to ongoing maintenance and troubleshooting.
The responsibilities of a Linux administrator are diverse and encompass a wide range of tasks. Here are some of the key duties you can expect to encounter in this role:
To excel as a Linux administrator, you'll need a diverse skill set and a solid foundation in both technical and soft skills. Here are some of the key skills and qualifications required for this role:
By honing these skills and qualifications, you'll be well-equipped to succeed in the dynamic and challenging field of Linux administration.
How to Answer: When addressing this question, candidates should demonstrate their understanding of the init process as the first process that starts when a Linux system boots up. They should explain its role in initializing the system, managing services, and transitioning to different runlevels. Candidates should highlight how init has evolved over time, particularly with the transition to systemd in modern Linux distributions.
Sample Answer: "The init process in Linux is the first process that starts when the system boots up. Its primary role is to initialize the system, manage services, and transition the system to different runlevels or states. In traditional Unix systems, init used to follow a sequential approach to start services, but with the adoption of systemd in many modern distributions, init has evolved to use parallelization for faster boot times and better service management."
What to Look For: Look for candidates who can articulate a clear understanding of the init process, its historical context, and its evolution with systemd. Strong candidates will demonstrate familiarity with different runlevels and the significance of init in managing system services.
How to Answer: Candidates should explain that sudo stands for "superuser do" and is used to execute commands with elevated privileges. They should emphasize its role in allowing authorized users to perform administrative tasks while providing a layer of security by logging commands and controlling access through configuration files like /etc/sudoers.
Sample Answer: "The sudo command in Linux allows users to execute commands with elevated privileges, typically those reserved for the root user. It's a crucial tool in system administration as it enables authorized users to perform administrative tasks while providing a layer of security by logging commands and controlling access through the /etc/sudoers configuration file. Sudo helps mitigate the risk of unauthorized access to critical system functions."
What to Look For: Look for candidates who can clearly articulate the purpose of sudo and its significance in managing system privileges. Strong candidates will demonstrate knowledge of sudo configuration and best practices for secure privilege escalation.
How to Answer: Candidates should differentiate between hard links, which are direct pointers to an inode on disk, and symbolic links, which are pointers to the path of a file. They should highlight the advantages and limitations of each type of link, including how they behave when the original file is moved or deleted.
Sample Answer: "Hard links and symbolic links are two types of links used in Linux file systems. A hard link is a direct pointer to an inode on disk, which means it shares the same inode number and data blocks as the original file. In contrast, a symbolic link is a separate file that contains the path to the target file. One advantage of hard links is that they can refer to files on the same file system, while symbolic links can point to files on different file systems. However, symbolic links are more flexible as they can point to directories and across file systems, whereas hard links cannot. Additionally, if the original file is moved or deleted, a symbolic link becomes broken, whereas a hard link remains intact."
What to Look For: Look for candidates who can clearly articulate the differences between hard links and symbolic links, including their advantages and limitations. Strong candidates will demonstrate an understanding of inode structures and how links interact with file system operations.
How to Answer: Candidates should explain that they can determine disk usage using commands like df (disk free) and du (disk usage). They should discuss the differences between these commands, with df providing an overview of filesystem usage and du providing more granular information about directory sizes.
Sample Answer: "To determine disk usage on a Linux system, I would use commands like df and du. The df command provides an overview of filesystem usage, showing details such as total space, used space, and available space for each mounted filesystem. On the other hand, the du command provides more granular information about directory sizes, allowing me to identify which directories are consuming the most disk space. I can use options like -h for human-readable output and -s for summary mode to display total disk usage for a specific directory."
What to Look For: Look for candidates who demonstrate familiarity with common disk usage commands and options. Strong candidates will explain the differences between df and du and when each command is most appropriate for analyzing disk space.
How to Answer: Candidates should explain that they can configure a static IP address by modifying network configuration files such as /etc/network/interfaces or /etc/sysconfig/network-scripts/ifcfg-eth0 (depending on the distribution). They should emphasize the importance of making changes persistent by updating the appropriate configuration file.
Sample Answer: "To configure a static IP address in Linux, I would typically modify network configuration files such as /etc/network/interfaces or /etc/sysconfig/network-scripts/ifcfg-eth0. Within these files, I would specify the desired IP address, netmask, gateway, and DNS servers. It's important to ensure that the changes are persistent across reboots by updating the appropriate configuration file and restarting the network service."
What to Look For: Look for candidates who can demonstrate the process of configuring a static IP address in Linux and making the change persistent across reboots. Strong candidates will show familiarity with network configuration files and understand the importance of persistence in network settings.
How to Answer: Candidates should discuss various security measures such as disabling root login, using key-based authentication, changing the default SSH port, and implementing firewall rules to restrict access. They should emphasize the importance of regularly updating SSH software to patch security vulnerabilities.
Sample Answer: "To secure an SSH server in a Linux environment, I would take several measures. Firstly, I would disable root login and create separate user accounts with sudo privileges for administrative tasks. Additionally, I would enforce key-based authentication to enhance security over password-based authentication. Changing the default SSH port can also help mitigate automated attacks. Implementing firewall rules using iptables or firewalld to restrict access to the SSH service based on IP addresses or networks is another important step. Lastly, I would regularly update the SSH software to patch any security vulnerabilities and keep the server secure."
What to Look For: Look for candidates who can articulate a comprehensive approach to securing an SSH server, including multiple layers of defense such as user authentication, network filtering, and software updates. Strong candidates will demonstrate awareness of common SSH security best practices.
How to Answer: Candidates should explain that they can check the status of a running process using commands like ps (process status) or top (task overview). They should discuss how to identify the process ID (PID) and use the kill command to terminate a process if necessary, either gracefully with SIGTERM or forcefully with SIGKILL.
Sample Answer: "To check the status of a running process in Linux, I would use commands like ps or top. These commands provide information about running processes, including their process IDs (PIDs), CPU and memory usage, and execution status. If I need to terminate a process, I would first identify its PID using ps or top and then use the kill command followed by the PID. By default, kill sends a SIGTERM signal to gracefully terminate the process, allowing it to clean up resources. If the process does not respond to SIGTERM or if immediate termination is necessary, I can use kill -9 to send a SIGKILL signal, forcing the process to terminate immediately."
What to Look For: Look for candidates who demonstrate proficiency in process management, including checking process status and terminating processes when necessary. Strong candidates will show familiarity with common process-related commands and signal handling.
How to Answer: Candidates should explain that process scheduling is the mechanism by which the operating system decides which process to execute next on the CPU. They should discuss different scheduling algorithms such as round-robin, first-come-first-served (FCFS), and priority-based scheduling, highlighting their advantages and limitations.
Sample Answer: "Process scheduling in Linux refers to the mechanism by which the operating system determines the order in which processes are executed on the CPU. One common scheduling algorithm is round-robin, where processes are executed in a cyclic manner with each process receiving a fixed time slice or quantum. Another approach is first-come-first-served (FCFS), where processes are executed in the order they arrive. Priority-based scheduling assigns priorities to processes, allowing higher-priority processes to execute before lower-priority ones. Each scheduling algorithm has its own advantages and limitations. For example, round-robin ensures fairness among processes but may not be suitable for real-time applications, while priority-based scheduling allows for priority levels to be adjusted dynamically but can lead to starvation of lower-priority processes."
What to Look For: Look for candidates who can explain the concept of process scheduling and discuss different scheduling algorithms in Linux. Strong candidates will demonstrate an understanding of the trade-offs involved in selecting an appropriate scheduling algorithm for different use cases.
How to Answer: Candidates should explain that they can install software packages in a Debian-based distribution like Ubuntu using the apt package manager. They should discuss commands like apt-get and aptitude for package installation, removal, and dependency resolution.
Sample Answer: "To install software packages in a Debian-based Linux distribution like Ubuntu, I would use the apt package manager. The apt-get command is commonly used for package installation, removal, and management. For example, to install a package named 'example', I would use the command 'sudo apt-get install example'. Apt-get automatically resolves dependencies and installs required packages. Alternatively, I could use the aptitude command, which provides a text-based interface for package management with additional features like dependency tracking and conflict resolution."
What to Look For: Look for candidates who demonstrate proficiency in package management using the apt package manager. Strong candidates will be familiar with common apt commands and understand how to install, remove, and update software packages in a Debian-based distribution.
How to Answer: Candidates should explain that package repositories are collections of software packages maintained by distribution vendors or third parties. They should discuss how repositories are used by package managers to download and install software packages. Candidates should also demonstrate how to add a new repository to a system using configuration files like /etc/apt/sources.list or by using command-line tools like add-apt-repository.
Sample Answer: "Package repositories in Linux are collections of software packages maintained by distribution vendors or third parties. Package managers use repositories to download and install software packages, ensuring that users have access to a wide range of applications. To add a new repository to a system, I would typically edit the configuration file located at /etc/apt/sources.list and add the repository URL along with the distribution codename. Alternatively, many distributions provide command-line tools like add-apt-repository, which simplifies the process by automatically updating the repository configuration and performing key management tasks."
What to Look For: Look for candidates who can explain the role of package repositories in Linux package management and demonstrate how to add a new repository to a system. Strong candidates will show familiarity with repository management tools and understand the importance of repository configuration in maintaining a system's software ecosystem.
How to Answer: Candidates should explain that the sysctl command is used to view, set, and modify kernel parameters at runtime. They should discuss how sysctl is used to adjust various aspects of kernel behavior, such as network settings, process management, and filesystem parameters.
Sample Answer: "The sysctl command in Linux is used to view, set, and modify kernel parameters at runtime. It allows administrators to adjust various aspects of kernel behavior, including network settings, process management, and filesystem parameters. For example, I can use sysctl to adjust the maximum number of open files allowed by the kernel or to tweak TCP/IP networking parameters for optimal performance. Sysctl provides a flexible way to fine-tune the system's behavior without requiring a kernel rebuild or system reboot."
What to Look For: Look for candidates who can demonstrate proficiency in kernel configuration and troubleshooting using the sysctl command. Strong candidates will be able to articulate the purpose of sysctl and provide examples of how it can be used to optimize system performance.
How to Answer: Candidates should discuss the steps involved in diagnosing and troubleshooting kernel panics, including examining log files like dmesg and syslog, analyzing core dump files, and using kernel debugging tools like kdump and crash.
Sample Answer: "When troubleshooting kernel panics in a Linux system, the first step is to examine log files such as dmesg and syslog to identify any error messages or warning signs leading up to the panic. These logs can provide valuable clues about the underlying cause of the kernel panic. Additionally, analyzing core dump files generated during the panic can help pinpoint the exact location and nature of the problem. Tools like kdump and crash are useful for analyzing core dumps and extracting relevant information about the state of the system at the time of the panic. By systematically gathering and analyzing diagnostic data, administrators can identify the root cause of kernel panics and take appropriate remedial actions."
What to Look For: Look for candidates who can explain the process of troubleshooting kernel panics in a Linux system and demonstrate familiarity with diagnostic techniques and tools. Strong candidates will emphasize the importance of systematic troubleshooting and data analysis in resolving kernel-related issues.
How to Answer: Candidates should explain that full backups involve copying all data in a system, incremental backups only copy data that has changed since the last backup, and differential backups copy all data that has changed since the last full backup. They should discuss the advantages and limitations of each backup type and when each type is typically used in backup strategies.
Sample Answer: "Full backups involve copying all data in a system, regardless of whether it has changed since the last backup. While full backups require more storage space and time to complete, they offer complete data redundancy and are often used as a baseline for other backup types. Incremental backups, on the other hand, only copy data that has changed since the last backup, which reduces storage space and backup time compared to full backups. However, restoring from incremental backups may require accessing multiple backup sets, which can be time-consuming. Differential backups copy all data that has changed since the last full backup, providing a middle ground between full and incremental backups. They require less storage space than full backups and are faster to restore from than incremental backups since only two backup sets are needed. Each type of backup has its own advantages and limitations, and the choice depends on factors such as storage capacity, backup window, and recovery time objectives."
What to Look For: Look for candidates who can explain the differences between full, incremental, and differential backups and when each type is typically used in backup strategies. Strong candidates will demonstrate an understanding of backup concepts and considerations for data redundancy and recovery.
How to Answer: Candidates should discuss the key components of a backup strategy, including defining data retention policies, determining backup frequency based on data criticality and recovery objectives, and implementing disaster recovery measures such as offsite backups and regular testing.
Sample Answer: "When designing a backup strategy for a Linux server environment, several factors need to be considered to ensure data protection and disaster recovery preparedness. Firstly, it's important to define data retention policies that specify how long backups should be retained based on regulatory requirements, business needs, and data criticality. Next, determining backup frequency involves assessing the rate of data change and the acceptable recovery point objectives (RPOs) for different systems and applications. Critical systems may require frequent backups, such as hourly or daily, while less critical data can be backed up less frequently. Disaster recovery measures should also be incorporated into the backup strategy, including offsite backups stored in geographically diverse locations to mitigate the risk of data loss due to localized disasters. Regular testing of backups and disaster recovery procedures is essential to ensure their effectiveness in real-world scenarios and to identify any gaps or weaknesses in the backup strategy."
What to Look For: Look for candidates who can design a comprehensive backup strategy for a Linux server environment, considering factors such as data retention policies, backup frequency, and disaster recovery measures. Strong candidates will demonstrate an understanding of backup best practices and the importance of regular testing and validation.
How to Answer: Candidates should discuss the advantages of using shell scripting for automation tasks, including increased efficiency, consistency, and scalability. They should highlight how shell scripts can automate repetitive tasks, reduce human error, and streamline system administration workflows.
Sample Answer: "Shell scripting is a powerful tool for automation tasks in a Linux environment, offering several benefits for system administrators. Firstly, shell scripts can automate repetitive tasks, such as file management, system monitoring, and software installations, saving time and effort compared to manual execution. By encapsulating commands and logic in scripts, administrators can ensure consistency and repeatability across different systems and environments. Shell scripts also enhance scalability by allowing administrators to automate complex workflows and orchestrate multiple tasks sequentially or in parallel. Additionally, shell scripting facilitates collaboration and knowledge sharing among team members, as scripts can be easily shared and reused to solve common problems. Overall, shell scripting is an essential skill for system administrators looking to streamline operations, reduce human error, and improve efficiency in managing Linux systems."
What to Look For: Look for candidates who can articulate the benefits of using shell scripting for automation tasks in a Linux environment. Strong candidates will demonstrate an understanding of how shell scripts can improve efficiency, consistency, and scalability in system administration workflows.
Looking to ace your next job interview? We've got you covered! Download our free PDF with the top 50 interview questions to prepare comprehensively and confidently. These questions are curated by industry experts to give you the edge you need.
Don't miss out on this opportunity to boost your interview skills. Get your free copy now!
Preparing for a Linux admin interview is crucial to ensuring you're ready to showcase your skills and expertise. Let's explore some essential steps you can take to prepare effectively for your interview.
Before your interview, it's essential to conduct thorough research on the company and its Linux environment. Understanding the company's products, services, and industry can give you valuable insights into how Linux is used within the organization. Here are some key areas to focus on during your research:
By conducting comprehensive research, you'll be better prepared to discuss how your skills and experience align with the company's needs and objectives during the interview.
To prepare for the technical aspect of your interview, it's essential to review common Linux admin interview questions. These questions cover a wide range of topics, including system administration, networking, security, and troubleshooting. Here are some examples of common Linux admin interview questions:
Practice answering these questions aloud and be prepared to explain your thought process and problem-solving approach during the interview.
In addition to reviewing interview questions, it's essential to practice your technical skills and scenarios to ensure you're well-prepared for the hands-on aspect of the interview. Set up a virtual lab environment using tools like VirtualBox or VMware and simulate real-world scenarios such as:
By practicing technical skills and scenarios, you'll build confidence and proficiency in handling real-world challenges, allowing you to perform at your best during the interview.
As a Linux administrator, possessing a diverse skill set and deep knowledge of various aspects of Linux systems is essential for success. Let's delve into the essential skills and knowledge areas that every Linux admin should master.
Linux administrators must be proficient in working with different Linux distributions, each with its own set of features, package management systems, and configurations. Some of the most common distributions include:
Linux administrators should have hands-on experience with installing, configuring, and maintaining servers running on different distributions, understanding their unique nuances and best practices.
The command line is a Linux administrator's primary interface for managing and administering systems. Proficiency in command-line tools and shell scripting is essential for performing tasks efficiently and automating repetitive tasks. Some key areas to focus on include:
ls, cd, pwd, and mkdir for navigating and manipulating files and directories.cp, mv, rm, and touch.ps, top, kill, and killall.Command-line proficiency is a fundamental skill for Linux administrators and is essential for efficiently managing Linux systems in various environments.
Networking is a critical aspect of Linux administration, as servers often serve as the backbone of network infrastructure. Linux administrators should have a solid understanding of networking fundamentals, including:
ping, traceroute, netstat, and tcpdump.By mastering networking fundamentals and troubleshooting techniques, Linux administrators can ensure the reliable and efficient operation of networked systems and services.
Security is a top priority for Linux administrators, given the importance of protecting systems and data from unauthorized access and cyber threats. Linux administrators should be well-versed in security best practices and techniques, including:
iptables or firewalld to control incoming and outgoing network traffic and protect against unauthorized access.By implementing robust security measures and staying vigilant against emerging threats, Linux administrators can safeguard their systems and data from potential security breaches.
Monitoring system performance and optimizing resource utilization are essential tasks for Linux administrators to ensure the smooth operation of systems and applications. Key areas of focus include:
syslog, journalctl, sar, top, and monitoring solutions like Nagios, Zabbix, or Prometheus to collect and analyze system logs and performance data.By effectively monitoring system performance and optimizing resource utilization, Linux administrators can proactively identify and address performance issues, ensuring the reliable and efficient operation of Linux-based systems and services.
Preparing for the technical aspect of a Linux admin interview requires a deep dive into various areas of Linux administration. Let's explore how you can effectively prepare for the technical interview.
The command line is the primary interface for interacting with Linux systems, making proficiency in command-line tools and utilities essential for Linux administrators. Here's how you can prepare:
ls, cd, pwd, mkdir, rm, cp, and mv for navigating the file system and managing files and directories.grep, sed, and awk for searching, replacing, and extracting data from text files.ps, top, kill, and nice for viewing running processes, prioritizing them, and terminating them if necessary.apt, yum, dnf, and zypper depending on the Linux distribution.uname, hostnamectl, df, free, and lscpu for retrieving system information such as kernel version, hostname, disk space usage, memory usage, and CPU information.By mastering these command-line tools and utilities, you'll be well-prepared to tackle technical questions and scenarios during the interview.
File systems and disk management are essential aspects of Linux administration, as they involve managing storage resources efficiently and ensuring data integrity. Here's what you should focus on:
fdisk, gdisk, or parted, and understand the differences between primary, extended, and logical partitions.mount and umount, and understand the /etc/fstab file for configuring persistent mounts.By mastering file systems and disk management concepts, you'll be able to effectively manage storage resources and ensure the reliability and performance of Linux systems.
Configuration management is crucial for automating system administration tasks and maintaining consistent configurations across multiple servers. Here's how you can prepare:
By mastering configuration management tools like Ansible, Puppet, or Chef, you'll be able to streamline and automate repetitive tasks, improve efficiency, and reduce the risk of configuration errors.
Virtualization and containerization technologies have revolutionized the way infrastructure is managed and deployed in modern IT environments. Here's what you should focus on:
By gaining familiarity with virtualization and containerization technologies like Docker and Kubernetes, you'll be better equipped to deploy and manage applications efficiently in modern cloud-native environments.
Troubleshooting is an essential skill for Linux administrators, as they often encounter a variety of technical issues in their day-to-day operations. Here's how you can prepare:
journalctl, syslog, and dmesg to identify errors, warnings, and other messages related to system and application events.ping, traceroute, and netstat.top, vmstat, sar, and iostat to identify performance bottlenecks such as high CPU usage, memory pressure, disk I/O, and network congestion.strace, lsof, and tcpdump to trace system calls, monitor open files, and capture network traffic.By developing strong troubleshooting skills and familiarity with diagnostic tools and techniques, you'll be able to effectively identify and resolve technical issues, ensuring the reliable and efficient operation of Linux servers and services.
In addition to technical expertise, soft skills and effective communication are essential for success as a Linux administrator. Let's explore the soft skills that are crucial in the field of Linux administration.
As a Linux administrator, you'll often need to communicate complex technical concepts to various stakeholders, including colleagues, clients, and management. Here's why effective communication is vital:
By honing your ability to communicate technical concepts effectively, you'll be better equipped to collaborate with colleagues, troubleshoot issues, and deliver successful outcomes.
Problem-solving and critical thinking are core skills for Linux administrators, as they often encounter complex technical challenges that require innovative solutions. Here's how these skills come into play:
By cultivating strong problem-solving and critical thinking skills, you'll be better prepared to tackle complex technical issues and adapt to evolving challenges in the dynamic field of Linux administration.
Linux administration is often a collaborative endeavor, requiring teamwork and cooperation among team members to achieve common goals. Here's why teamwork is essential:
By fostering a culture of teamwork and collaboration within your team, you'll create an environment where everyone feels valued, motivated, and empowered to contribute their best work.
The field of Linux administration is constantly evolving, with new technologies, tools, and challenges emerging regularly. Here's why adaptability is crucial:
By cultivating adaptability and embracing change, you'll be better equipped to navigate the ever-changing landscape of Linux administration and thrive in dynamic and challenging environments.
On the day of your Linux admin interview, it's essential to be well-prepared and confident. Here are some tips and strategies to help you make a positive impression:
By following these tips and strategies, you'll be well-prepared to navigate the interview process with confidence and professionalism, increasing your chances of success in securing the Linux admin role.
Mastering Linux admin interview questions is the key to unlocking exciting opportunities in the field of Linux administration. By honing your technical skills, problem-solving abilities, and communication strategies, you'll be well-equipped to navigate the interview process with confidence and professionalism. Remember to showcase your expertise, demonstrate your enthusiasm for the role, and approach each interview as an opportunity to learn and grow. With the knowledge and insights gained from this guide, you're now ready to tackle any interview challenge and embark on a rewarding career journey as a Linux administrator.
As you prepare for your interviews, keep in mind that success is not just about answering questions correctly, but also about showcasing your passion, adaptability, and commitment to excellence. By leveraging the tips, strategies, and resources provided in this guide, you'll be able to stand out as a top candidate and secure your place in the dynamic and ever-growing field of Linux administration. So, go forth with confidence, seize every opportunity, and let your passion for Linux shine through in every interview. Your future as a successful Linux administrator awaits!